Mac Tweak Pro removal is important because it is a malicious app that doesn’t ask for permission to be installed and its scan results aren’t trustworthy.
When it comes to rogue software haunting Apple Macs, the usual suspects are apps representing the lineage that kicked off with Advanced Mac Cleaner, a scareware that became the progenitor of this trend. All of the follow-up junk programs from this family follow suit in terms of the distribution mechanisms, GUI design, and brainwashing techniques. This is precisely the case with Mac Tweak Pro, the latest offspring of said syndicate. It debuted as a PUA (potentially unwanted application) called Mac Tweak in early January 2019 and has since evolved into a predatory tool with the “Pro” component in its name. This adjustment didn’t turn out game-changing in any way, though – it’s still the same garden-variety rogue optimization and security solution. Let’s have a glance at what this culprit does, how its propagation takes place, and which approach bodes best for removing it from an infected system.

The activity of Mac Tweak Pro is all about scans and popup alerts that don’t seem to stop splashing out of the blue. However, the very first time this unwelcome program touches the victim’s computing experience, it may give a delusively nice impression. It looks well-tailored and sports an intuitive interface where everything seems to be where it belongs. The feature set is broken down into three sections, namely Cleaners, Utilities, and File Managers – each one listing several self-explanatory functions. The lullabying neatness of the application is just the tip of the iceberg. What lies beneath this whole appeal is a cyber impostor that generates fake warnings and may even get aggressive at times.
Every time Mac Tweak Pro completes a computer scan and returns the results, it reports a heap of junk data, unnecessary logs, cache, unused language packages, as well as duplicate and large files. Additionally, it will try to give the victim an extra heads-up by claiming to have detected rogue apps (which it is itself, by the way) and other security issues. Furthermore, the shady program displays the improvement potential for different areas, and it is mostly flagged “high” to encourage the user to take action right away.
Mac Tweak Pro may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.What is it that Mac Tweak Pro wants the victim to do at the end of the day? The answer has been invariable with all iterations of this rogue software species – it’s about money. By reporting phony performance problems and inexistent security threats, it tries to pressure the user into registering the tool to “fix all issues”. The activation, obviously, takes place on a payment basis. If the Mac user lingers with the decision, the pest will be shelling them with a growing number of reminders that come in the form of nag screens, popup alerts, or even browser redirects leading to counterfeit warning or tech support sites. Speaking of the latter, the infection chain actually begins at the level of web surfing. One of the primary vectors of contamination involves a series of browser rerouting instances that are triggered when the to-be victim visits a hacked or malicious site setup specifically to spread the malware.
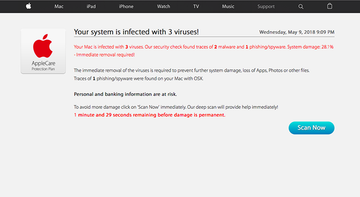
A common online fraud aimed at pushing Mac Tweak Pro has to do with a deceptive page that says the visitor’s system is heavily damaged and “infected with 3 viruses”. It may even estimate the scope of this damage at 33.2%, an identical figure for all people who end up on the scam site. Underscoring the purported fact that the user’s personal and banking information is at risk and that literally a few minutes remain before the damage is permanent, the page coerces them to hit the Scan Now button. If the hoax works out, the Mac Tweak Pro scareware will be installed onto the computer, only to commence its dodgy routine described above.
To wrap up, Mac Tweak Pro is a hostile application comparable to a wolf in sheep’s clothing. It enters systems by fraudulent means and inflates the victim’s day-to-day digital life with exaggerated or outright fake scan reports. This way, the culprit attempts to hoodwink the user into coughing up a fee for its license. None of these is what a normal program would ever do, therefore eliminating the malicious app under scrutiny is on the to-do list of every person whose Mac has been attacked in such a fashion.
Mac Tweak Pro virus manual removal for Mac
The steps listed below will walk you through the removal of this potentially unwanted application. Be sure to follow the instructions in the order specified.
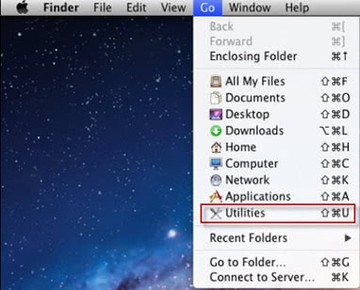
- Open up the Utilities folder as shown below
- Locate the Activity Monitor icon on the screen and double-click on it
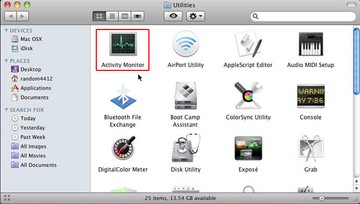
- Under Activity Monitor, find the entry for Mac Tweak Pro, select it and click Quit Process
- A dialog should pop up, asking if you are sure you would like to quit the Mac Tweak Pro executable. Select the Force Quit option
- Expand the Go menu in Apple Finder and select Go to Folder
- Type or paste the following string in the folder search dialog: /Library/LaunchAgents
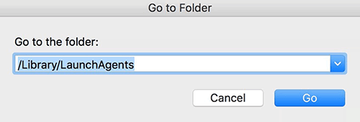
- Once the LaunchAgentsdirectory opens up, find the following entries in it and move them to Trash:
- com.MacTweakPro.agent.plist
- com.MTP.agent.plist
- com.MacTweakPro.msphlpr
- com.MTP.msphlpr
- Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/LaunchAgents. When this path opens, look for the same entries (see above) and send them to Trash
- Similarly, go to the ~Library/Application Support folder. Locate and move the following entries to Trash:
- MacTweakPro
- helpermtp
- hlprmtp
- hlprmactweakpro
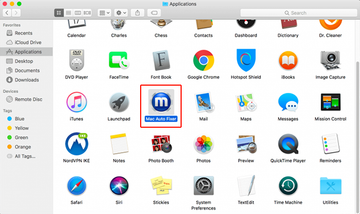
- Click the Go button again, but this time select Applications on the list. Find the entry for Mac Tweak Pro on the interface, right-click on it and select Move to Trash. If user password is required, go ahead and enter it
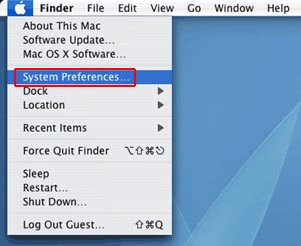
- Now go to Apple Menu and pick the System Preferences option
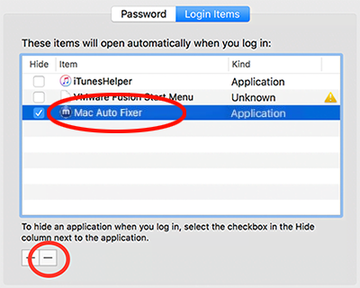
- Select Accounts and click the Login Items button. The system will come up with the list of the items that launch when the box is started up. Locate Mac Tweak Pro there and click on the “-“ button
Use automatic tool to uninstall Mac Tweak Pro virus from your Mac
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Mac Tweak Pro virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Mac Tweak Pro issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Mac Tweak Pro threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
